Driver Accountability Layer
Authorised Drivers Only. No Exceptions.
Enforce fleet access policies with facial recognition, RFID, PIN, or app-based login.
When anyone can start the engine, everything’s at risk.
Why Unauthorized Vehicle Use Matters
When anyone can start a fleet vehicle without verification, it’s more than a policy breach — it’s a direct threat to safety, compliance, and your bottom line. Driver authentication puts you in control before the journey even begins, helping you prevent misuse, ensure compliance, and protect your operations.
Theft & Misuse
Without authentication, vehicles are vulnerable to being stolen, misused, or taken for personal errands — often without you knowing until damage is done.
Operational Disruption
Unauthorized use can delay jobs, disrupt delivery schedules, or compromise emergency response efforts — affecting customer satisfaction and trust.
Compliance Violations
In regulated industries, failing to restrict vehicle access to approved personnel can lead to costly fines, audits, and legal consequences.
Insurance & Liability Exposure
If an unapproved driver is involved in an accident, insurers may reject the claim — placing the financial burden squarely on your company.
Accountability Gaps
Without proper identity logs, it’s harder to trace incidents like speeding, reckless driving, or tampering — making driver training and accountability more challenging.
Fleet Downtime & Wastage
Unauthorized use can lead to unexpected breakdowns, unnecessary fuel consumption, and unplanned maintenance — draining resources and reducing overall fleet efficiency.
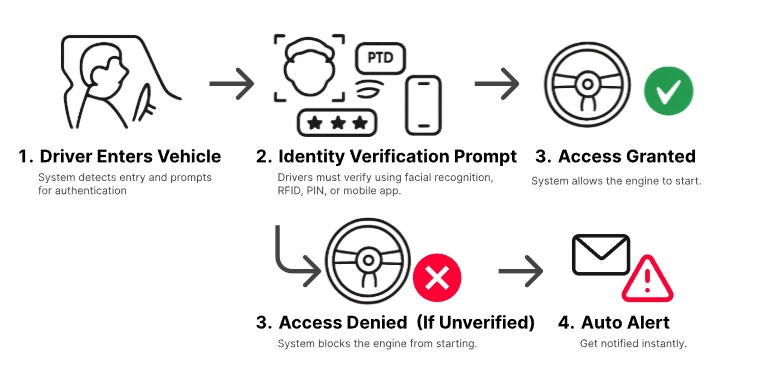
How Identity-Based Vehicle Access Works
Identity-based access control that verifies drivers before ignition —
ensuring only authorized personnel can operate fleet vehicles.
ensuring only authorized personnel can operate fleet vehicles.
Driver Identity Logs
All driver access attempts are logged with name, method, time, and outcome. Get a clear audit trail of who, when, and how — even for failed or unauthorized attempts. These logs help improve accountability, driver coaching, and compliance.
Timestamp
Driver Name
Method
Status
2026-02-15 07:43
Jason
Facial
Success
2026-02-15 08:12
Matthew
Facial
Success
2026-02-15 18:51
Unknown
Tag
Failed
2026-02-15 21:19
Unknown
RFID
Failed
2026-02-15 22:50
Ben
Tag
Success
Basic plan
$96/year
Basic features for up to 10 users with everything you need.
Get started
Business plan
$192/year
Advanced features and reporting, better workflows and automation.
Get started
Enterprise plan
$384/year
Personalised service and enterprise security for large teams.
Get started
User access
Basic features
Saved reports
10
20
Unlimited
Individual data
20GB
40GB
Unlimited
Support
Automated workflows
200+ integrations
Reporting and analytics
Analytics
Basic
Advanced
Advanced
Export reports
Scheduled reports
API access
Advanced reports
Saved reports
Customer properties
Custom fields
User access
SSO/SAML authentication
Advanced permissions
Audit log
Data history
Frequently asked questions
Everything you need to know about Driver Authentication and vehicle access control.
Can a vehicle be shut down while moving?
Installation typically takes under 2 hours per vehicle, depending on make/model and configuration. We schedule installs to minimise downtime.
Can I manage multiple drivers per vehicle?
Yes. You can assign multiple authorised drivers to the same vehicle. Every access attempt is logged per driver for accountability.
Can I control driver access by time or location?
Yes. Set time windows (e.g., after-hours lockout) and location rules / geofencing to restrict when and where a vehicle can be started.
Can a vehicle be shut down while it’s moving?
No. For safety, immobilisation is designed to activate only when the vehicle is stationary or below a predefined low-speed threshold (configuration dependent). The system verifies vehicle status before applying control.
What happens if someone tries to bypass or tamper with the system?
Tamper or power-disconnect attempts trigger real-time alerts. Depending on configuration, the vehicle can remain engine-disabled until released by an authorised admin.
What if the vehicle is offline or out of coverage?
If connectivity is temporarily unavailable, events are stored and synced once the vehicle regains signal. Optional local rules can continue enforcing access policies even during short outages (vehicle/model dependent).
Will this void my vehicle warranty?
Installation is performed professionally and compatibility is verified before deployment. Where supported, we use non-invasive methods. If you have specific warranty constraints, we’ll advise the best approach for your vehicle model.
Are driver identity logs available for audits or investigations?
Yes. Access attempts are logged with driver identity, method, timestamp, vehicle, and outcome (approved/denied/failed). Logs support compliance reviews, incident investigations, and driver coaching.
How is driver data protected (especially facial recognition)?
Driver identity data is handled with controlled access and security measures. We can align deployment with your internal policies and relevant data protection requirements. (Exact implementation depends on configuration and chosen authentication method.)
Is ongoing support available?
Yes. We provide local support, system health monitoring, and firmware updates to keep the system reliable and ready for day-to-day operations.





